PWK(OSCP) [PEN-200] Review 2021
This short blog post covers how I approached Offensive Security’s PEN-200 coursework along with the examination.

Pre-PWK Preparation
I started my preparation from Proving Grounds Practice (19$/month). It is absolutely worth spending money on, as it provides non-CTF style boxes curated by Offsec itself. I was able to solve 32 boxes (did TJ Null’s PG practice list) in a month, spending 4–5 hours, 5 days/week. After my subscription expired, I revised buffer overflow and curated Linux/Windows privesc cheatsheets for a week.
PEN-200 Coursework
I registered for a 30 days voucher + 1 exam attempt.
Starting with the coursework pdf, it took me 3 days to go over all the modules. Next, I began pwning the machines on the PWK network. I was able to root 70 machines in 25 days including 2–3 break days. On average I was solving 4–5 machines daily and it felt like I was giving the exam every day XD
I preferred spending the last week revising my notes, building a better methodology, and therefore, left the remaining 5 boxes. I completed a few lab exercises but did not document them for the extra 5 points as it was time-consuming for 30 days of access. I spent most of my time on the PWK network.
Note: During lab time, I used to spend 90–100 hours a week and was not working on anything else.
The OSCP exam
My lab access expired on 6th July 2021 and I scheduled my exam for the same day itself.
My Exam Methodology
I came up with the following strategy:
- complete buffer overflow in the first hour while enumerating the 10 pointer
- hit the 10 pointer machine for the next 1 hour, while enumerating the 20 pointers
- if the 10 pointer box is solved, move on to the 20 point box with a lower number of ports (because in that case, I’ll have to focus on less)
- at last, enumerate the 25 pointer box
I planned to take 10 min breaks every time I solved a box or after being stuck for 2 hours straight.
1 Day before the exam
I did the Try Hack Me rooms for buffer overflow, Linux and Windows privesc in the first part of the day (for the second time). Next, I spent my time watching movies and tv shows.
The final Exam day
On 6th July, I woke up at 7 a.m and went to exercise for 30 minutes. My exam was scheduled for 8:30 a.m. As required, I connected to the proctoring tool 15 minutes before the exam. Finally, the exam began and it went in the following order:
- Buffer overflow (25 points) [20 minutes]
- 10 point box [40 minutes]
- First 20 point box [1 hour 20 minutes]
- 25 point box (unintended root) [3 hours]
- Second 20 point box (1 hour)
- 25 point box (intended privesc) [10 minutes]
In the first 3 hours, I had 55 points with 3 boxes solved. Next, I tried the other 20 point box and I failed to find a foothold. I took a 1-hour long break and started with the 25 point box. It took me 2 hours to get a foothold and then I was stuck on the privesc for an hour. I finally managed to root it using an unintended method. In 7 hours, I had 80 points which were more than enough to pass the exam. After a short break, I started with the second 20 point box. It took me 45 minutes to get a rev-shell and 15 minutes to perform the privesc.
Technically, I was done with the exam, but I still wanted to find the intended root on the 25 point box. I manually performed the enumeration for privesc and found a potential vector. It took me another 10 minutes to get the root. Finally, I was done with the exam in 11 hours 30 minutes!
In short, it took me 7 hours to reach passing marks, 10 hours to root all the machines and 11 hours 30 minutes to solve everything in an intended way.
I took a 3-hour long break and then started with the report writing. Around 5 am in morning, I was done with a 45-page long report. I told my proctor to end the session and I finally went to sleep. The next morning, I proofread my report and uploaded it on the portal.
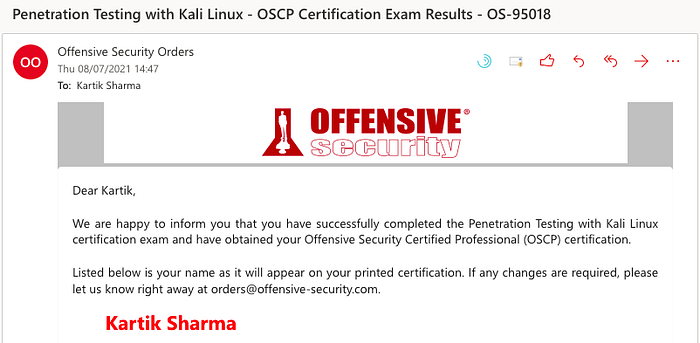
On 8th July, around 3 p.m, I received the e-mail!